Discord is an American chat app built for creating public and private communities. Initially developed as a platform for gamers to chat and call each other, the app has since grown to acquire 250 million registered users, as reported in 2019. Channels within Discord servers can be used for voice calls, video calls, chats, streaming, and file sharing. Channel visibility and access can be limited to invite-only. Considering these features, it is no surprise that Discord garnered the attention of the darknet market and attracted hackers, cybercriminals, child predators, supremacists, and neo-Nazis.
According to a Forbes article, in 2019 the FBI investigated a case involving the sharing of stolen data via Discord channels. In another case reported by CBS News, cybercriminals used Discord as an online shop to sell illicit products, such as stolen credit card numbers, cracked customer accounts for Delta Air Lines, Hilton Hotels, and much more. Unfortunately, examples like these continue to take place. Let’s have a look at how investigators can properly conduct a Discord investigation and acquire all the digital evidence they need using Oxygen Forensic® Detective.
Data extraction from mobile devices
For a Discord extraction from Apple iOS devices, we recommend a full file system via checkm8 or extraction of a jailbroken device in Oxygen Forensic® Detective.
To extract Discord from an Android device, investigators will need to have either a file system extraction or physical dump. Oxygen Forensic® Detective offers various extraction methods for both locked and unlocked Android devices.
In both cases, investigators can expect to extract the account info, contacts, direct messages, and channels from Apple iOS and Android devices.
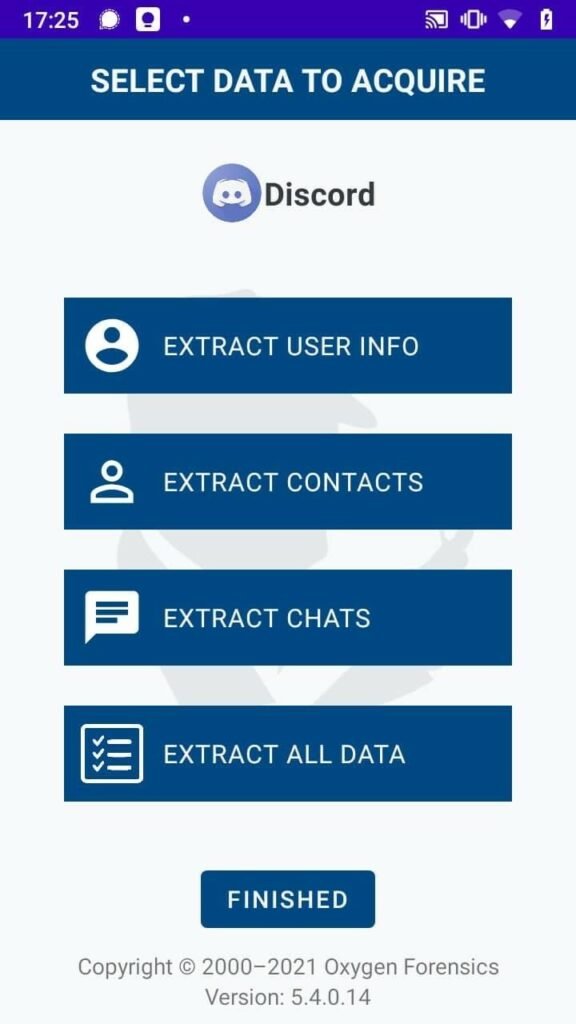
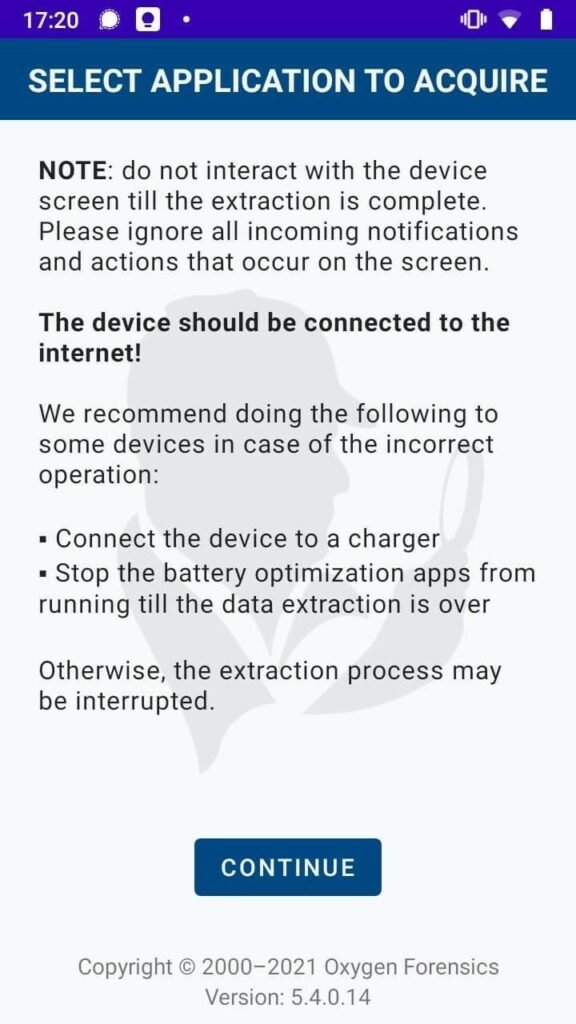
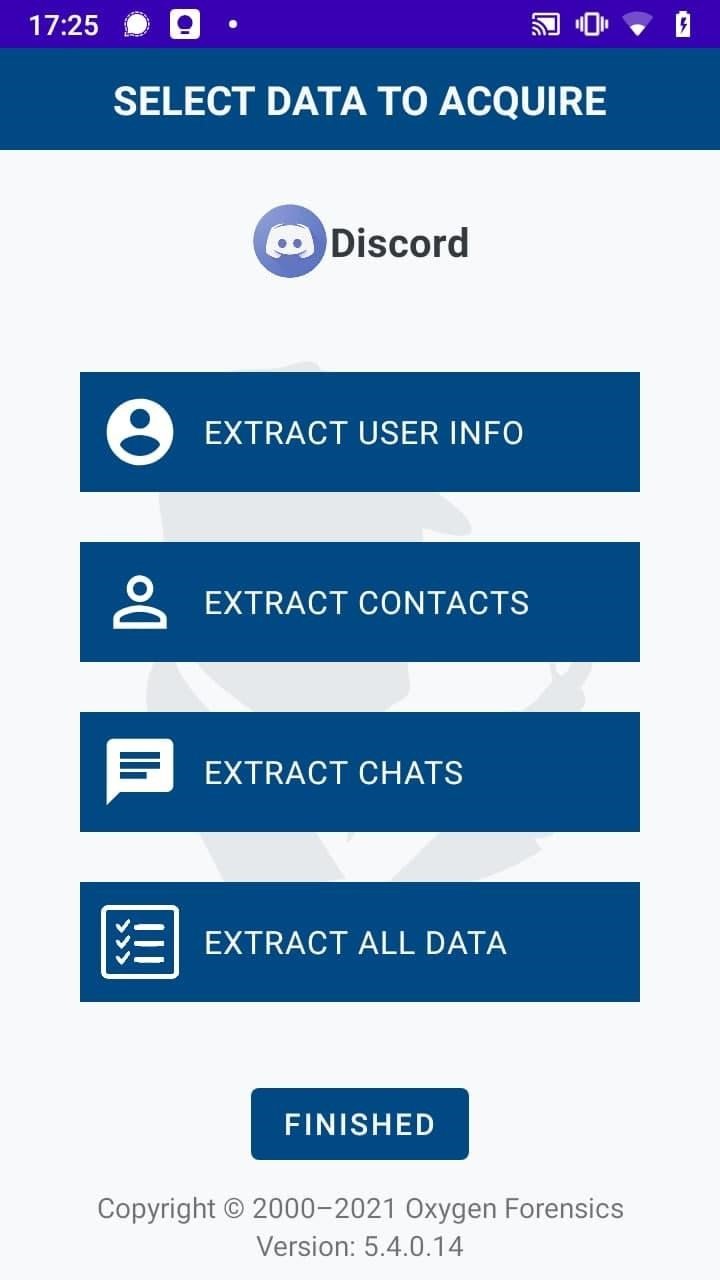
A new method of Discord data extraction has been implemented in our latest update, Oxygen Forensic®Detective v.13.4. Now investigators can collect all Discord data from any unlocked Android device using OxyAgent. Once OxyAgent is installed on a device, there are two requirements to follow before extraction:
- There must be an internet connection.
- Accessibility settings must be enabled in OxyAgent settings.
Collected data will include account info, contacts, private chats, group chats, and channels. This new method is useful when investigators need to conduct fast data collection and standard extraction methods do not work.
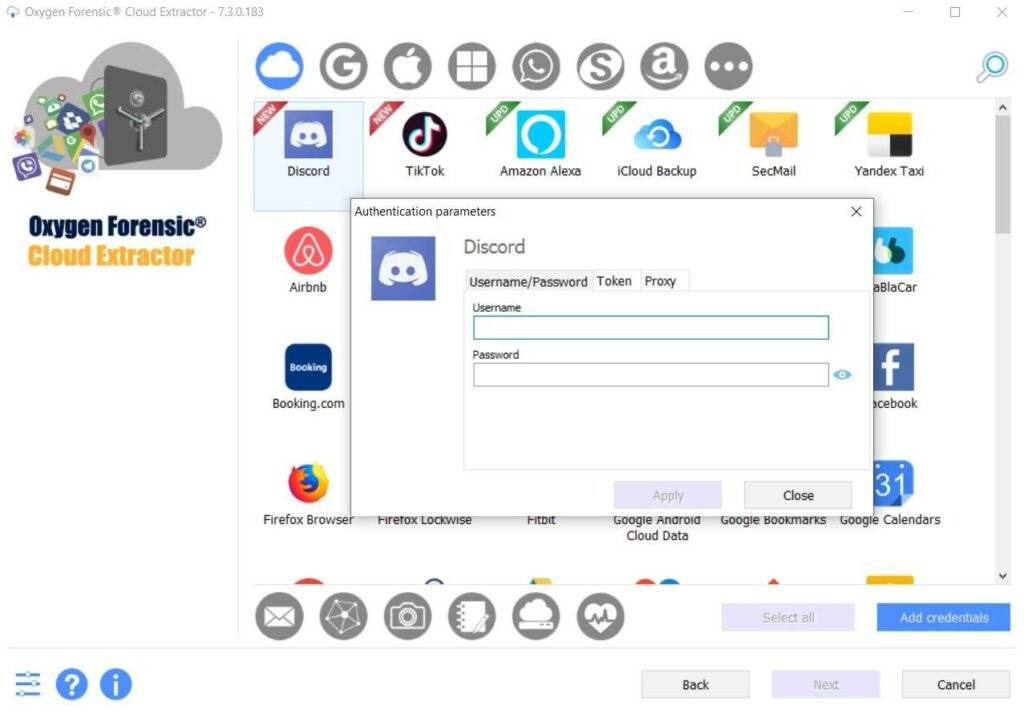
Cloud data extraction
Cloud extraction is an alternative method of Discord data extraction. Investigators can authorize Discord using the account’s login and password. If necessary, the investigator also has the ability to configure Proxy. If 2FA is set, an investigator can enter an authenticator code or a code received via SMS to the connected phone number. Similar to other extraction methods, extracted evidence will include account info, contacts, private chats, group chats, server information, channels, and settings.
Data extraction from computers
Because the Discord app on Windows and macOS does not store very much data, running our Oxygen Forensic® KeyScout will give investigators access to account info, cached files, and authentication tokens. This token can be used to extract complete Discord data in our Oxygen Forensic® Cloud Extractor. If Discord is used in a web browser, a token will be also extracted using Oxygen Forensic® KeyScout.

While some people choose to take advantage of the platform, there are many channels created to serve as helpful discussion boards on Discord. For example, the Digital Forensics Discord Server is a great DFIR community meeting point to communicate helpful advice and share experiences with peers. Additionally, the Oxygen Forensics support team is also here to help with any questions or challenges.
Oxygen Forensic® Detective v.13.4 provides unrivaled support for Discord investigations. To try Oxygen Forensic® Detective v.13.4, request a fully-featured demo license today.