Access to a device’s email can give investigators an upper hand in investigating all sorts of crime, especially corporate cases. Employees leaking sensitive data to competitors, harassing co-workers, hinting at blackmail or IP theft – these activities leave traces of data in their emails, which later become invaluable sources of evidence.
Oxygen Forensic® Cloud Extractor grants investigators access to all of this data with only a few clicks. Extract potential evidence from all main email clients, including Gmail, Outlook Mail, generic mail accounts (IMAP), QQ Mail and even the super-secure SecMail. Some of these services are not supported by our competitors, which is what makes the built-in Oxygen Forensic® Cloud Extractor an even better choice for analyzing mail data.
Let’s take a closer look at all the email services supported by Oxygen Forensic® Cloud Extractor!
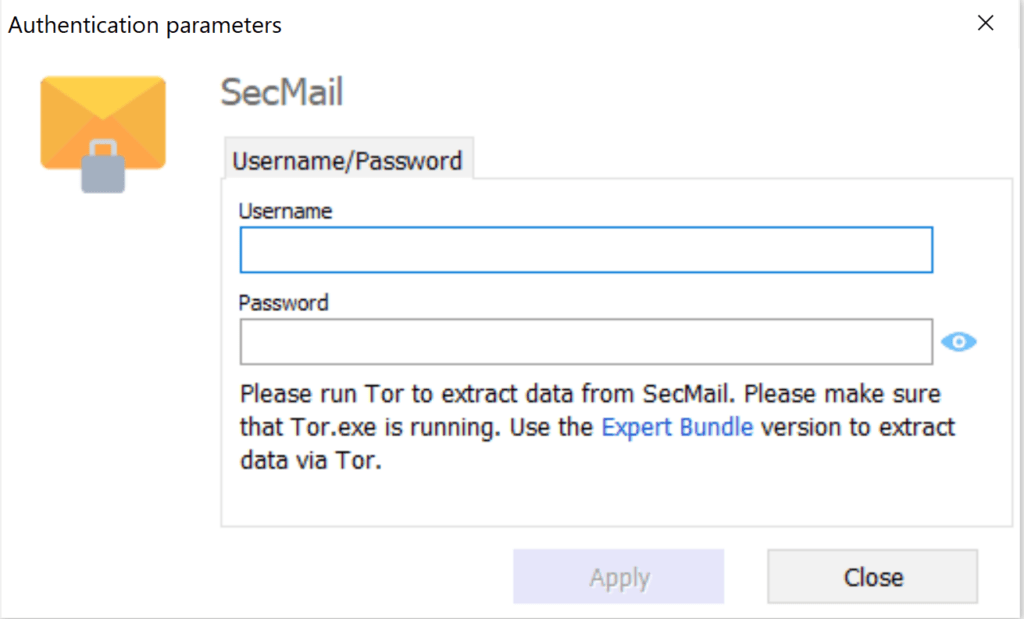
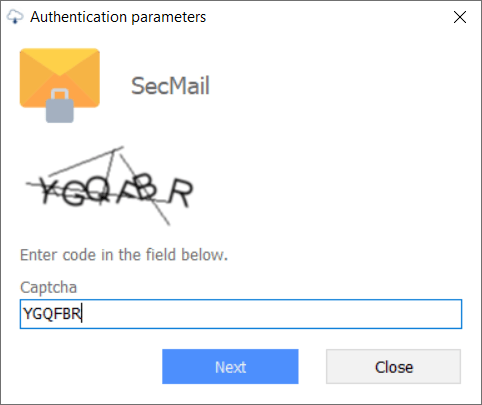
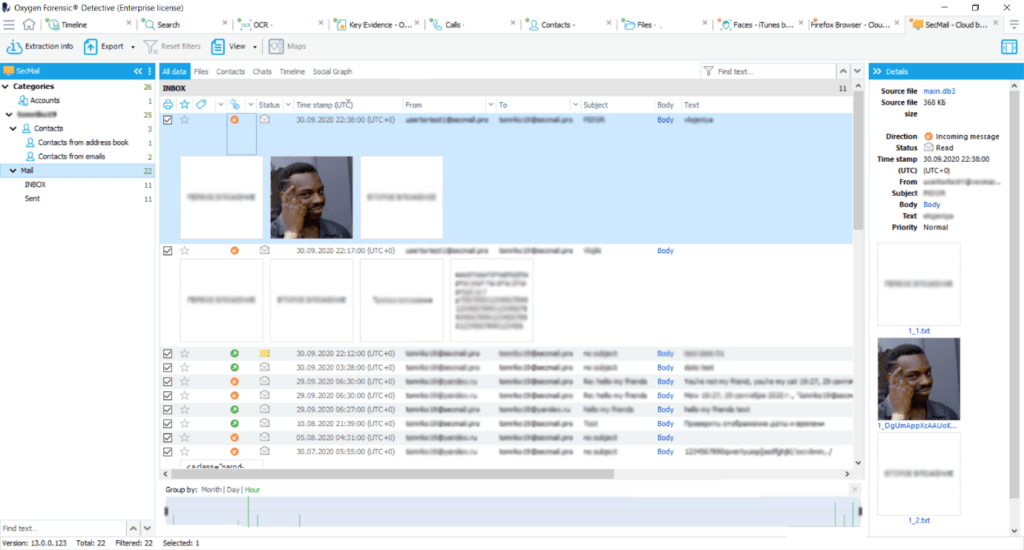
SecMail
SecMail is an extra secure and anonymous email service that is used to interact with people and organizations on the deep web. It can be set up using Tor browser. Investigators will need to run Tor in order to extract data from SecMail. Unfortunately, Tor does not have an app of its own, so user credentials are necessary to authorize in this service.
SecMail does not require two-factor-authorization. Therefore, as soon as a user enters the appropriate login credentials and CAPTCHA code, they can begin extracting the user’s account information, email contacts, address book contacts, and mail itself.
Google Mail
Google Mail is one of the most popular and widely used email clients. Data extraction from its cloud is supported by Oxygen Forensic® Cloud Extractor, which is built-into Oxygen Forensic® Detective. To authorize, investigators will need user credentials, a service token extracted from an Android device, or the master token. It should be noted, investigators can import credentials and tokens into Oxygen Forensic® Cloud Extractor straight from the Accounts and Password section in Oxygen Forensic Detective, as well as configure a proxy for the extraction.
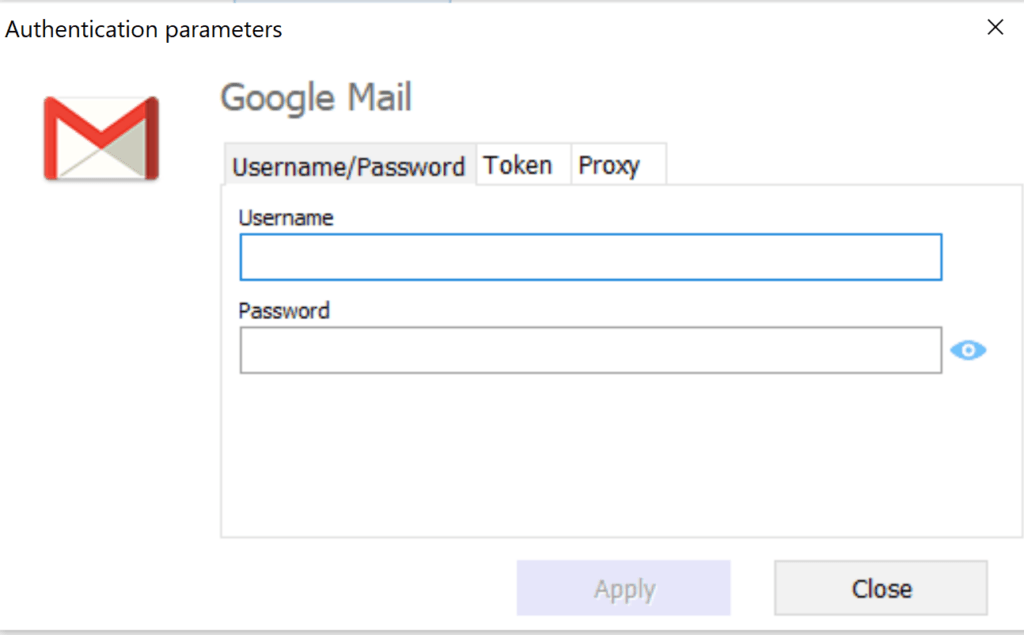
If two-factor-authorization is enabled, it can be bypassed by entering either an SMS code, a code sent to a backup email address stated by the account owner, or a code from the Google Authenticator app. Once the verification process is complete, investigators can proceed to extract the user’s account information, contacts, and mail, with all attachments.
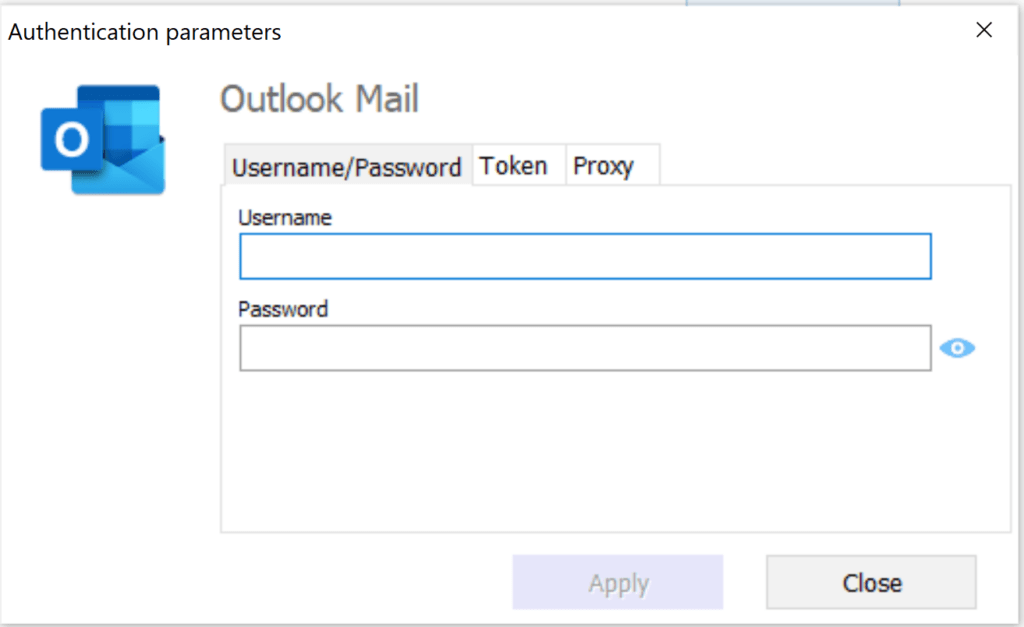
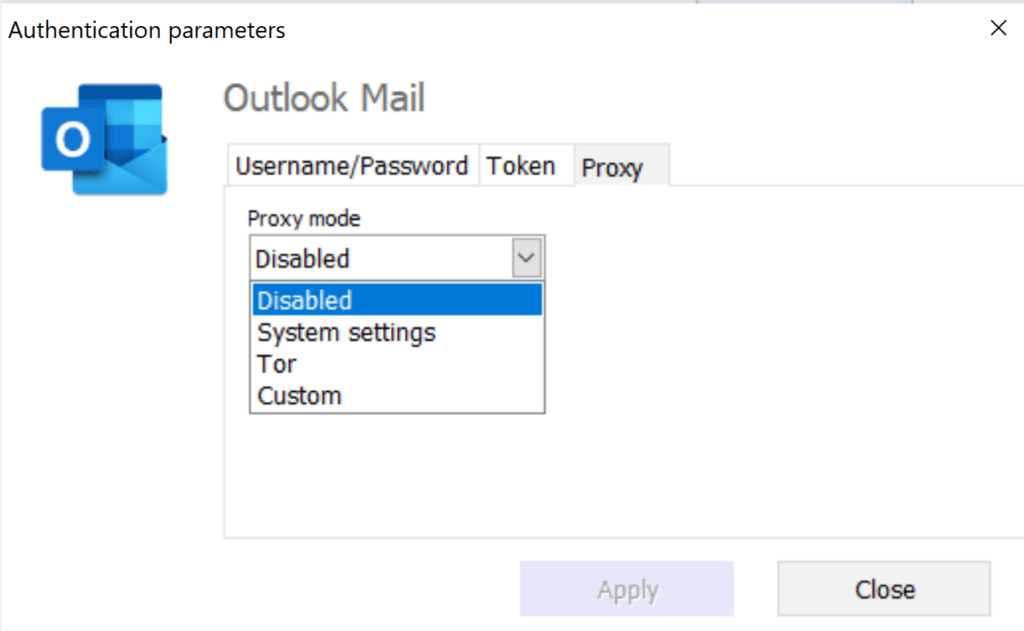
Outlook Mail
Outlook Mail is a personal information manager and web application from Microsoft consisting of webmail, calendar, contacts, and task services. It is the most popular desktop email client, ahead of Apple Mail and the 3rd most popular email client overall. To authorize, investigators will need Microsoft credentials, a generated token, or the token extracted from an iOS or Android device. Investigators can also import service credentials and tokens from the extraction’s Accounts and Passwords section in Oxygen Forensic® Detective. Additionally, users can configure and use a proxy during data extraction.
Like Google Mail, if two-factor-authorization is enabled, investigators can pass it by either entering an SMS code, a backup code, or a code sent to the Google Authenticator app. Once the investigator is logged in and verified, they can proceed to extract the user’s account information and mail.
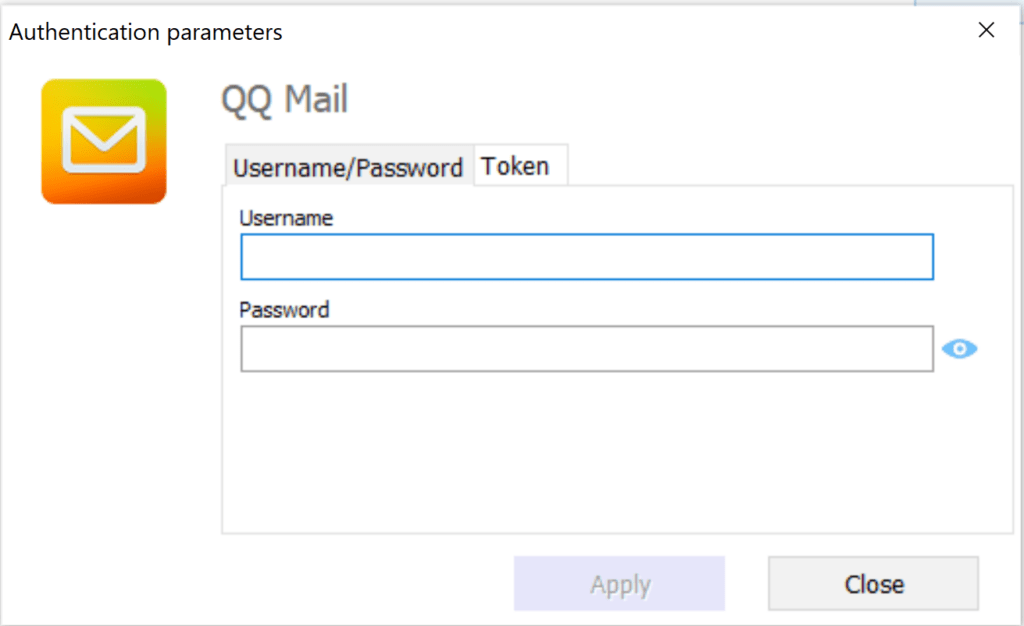
QQ Mail
QQ Mail, which is owned by the Chinese tech giant, Tencent, is both a messaging application and an email client. In China and parts of Asia, qq.com is like what gmail.com, yahoo.com, or outlook.com are to the US, in terms of providing email, messaging, and communication services.
To perform an authorization within this service, investigators will need to know the user’s login credentials or have an authentication token. Two- factor authorization is not necessary. Therefore, once the credentials are verified, Oxygen Forensic® Cloud Extractor will proceed to extract data from this service, including information regarding the account owner, their contacts, folders, and mail, including the attachments.
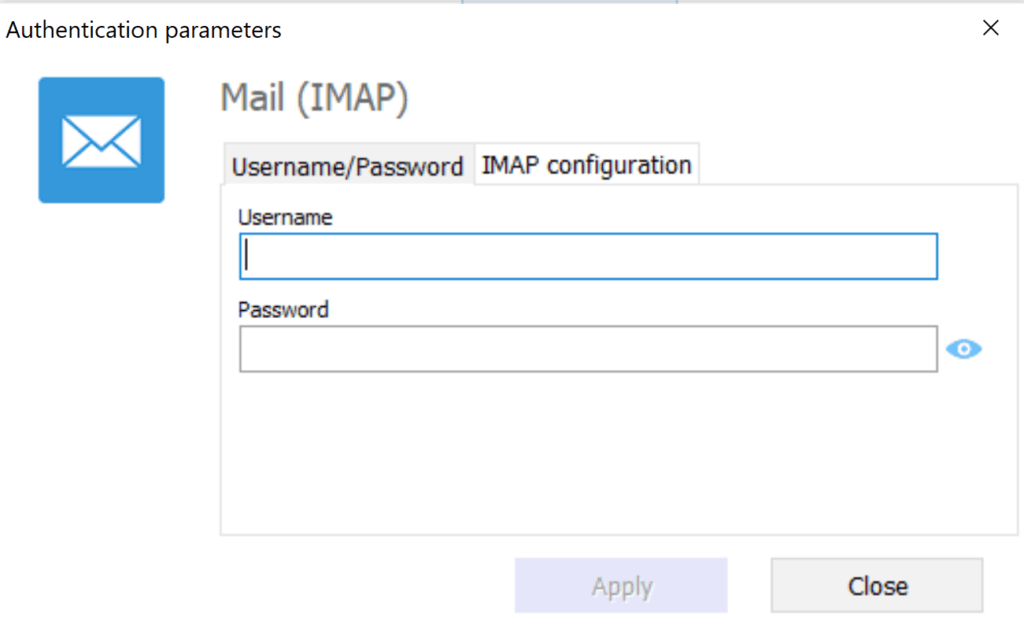
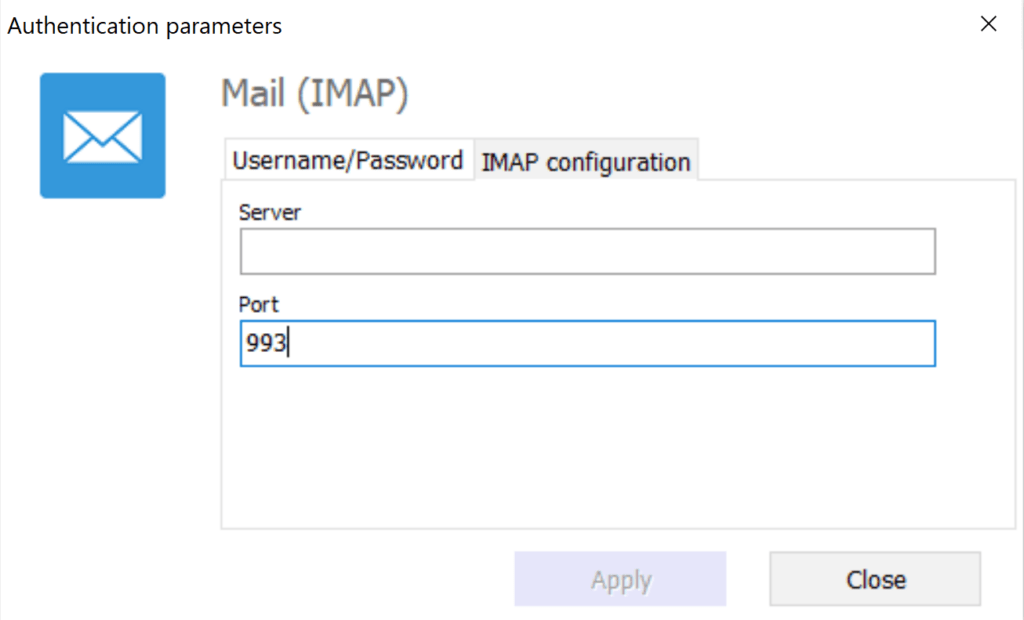
Mail (IMAP)
IMAP, or the Internet Message Access Protocol, is an Internet standard protocol used by email clients to retrieve email messages from a mail server over a TCP/IP connection. Knowing the user’s IMAP configurations and login credentials, investigators are able to extract all mail from the cloud, simply by using our Oxygen Forensic® Cloud Extractor. As soon as the extraction is complete, investigators can begin to import the results to Oxygen Forensic® Detective for further analysis!
With Oxygen Forensic® Detective, any evidence an investigator may require , be it personal or corporate, is just a few clicks away. Wish to try it? Ask for a demo license here.